SketchCop® is an authorized distributor for the f2 Face Forensics suite of facial recognition and image products developed by Face Forensics Inc., a private Canadian company headquartered in Vancouver, Canada.
The f2 team comprises professionals with years of combined experience in imaging technologies and applications, mathematics, biometrics, information technology, and international business.
Early in their career, they developed the UK’s ChildBase system, which at the time was the world’s largest pedophilic database face recognition system.
They continued their work to develop one of North America’s most successful face recognition systems. Law enforcement has enjoyed remarkable success using what has evolved into a robust suite of facial and object recognition tools, benefitting the public and private sectors.
F2’s strength in its scalability makes it an attractive, cost-effective crime-solving tool for law enforcement and, for the private sector, an effective tool in helping combat employee fraud.
This unique application combines f2’s full and partial face recognition, full and partial tattoo recognition, and corpse identification technology to aid in identifying disaster victims.
With f2’s Disaster Victim Identification (DVI) module, users can create databases of missing and unidentified persons or connect to existing HR systems (in read-only mode) using a copy of Microsoft SQL Server Express. (Included with the software.)
There is no limit to the number of victims that the system can work with.
Database information should include, but not be limited to, a frontal photo, personal data, and the name of a contact person or nearest relative.
Having a complete set of photographs and identifying information allows authorities to recover and identify deceased persons more quickly. f2’s DVI module can be integrated into an existing system or used as a stand-alone/networked application.
Full Face Recognition Face Forensics (f2) is a highly advanced face/facial recognition system designed to work with embedded or linked face images in your existing database, be it SQL Server, Oracle, or DB2.
f2 analyzes the characteristics of each image. The results form a unique digital encoding that describes each face. These encodings are stored in a separate database or matching gallery. Once f2 enrolls all the faces, new faces are registered and compared against those in the matching gallery.
f2 users can share matching galleries, allowing multiple users to connect to one gallery. Users can connect to any computer running an f2 gallery of interest. Searches compare encodings describing faces rather than images, making them extremely fast, typically greater than 1m records/second.
f2 can optimize itself for the specific type of image it’s being used to recognize. f2 is unaffected by race, age, or color.
During screening, f2 can analyze a variety of images from still photos and video sources. Users can send detection and recognition results to designated recipients, interactively or in a fully automated mode, as selected.
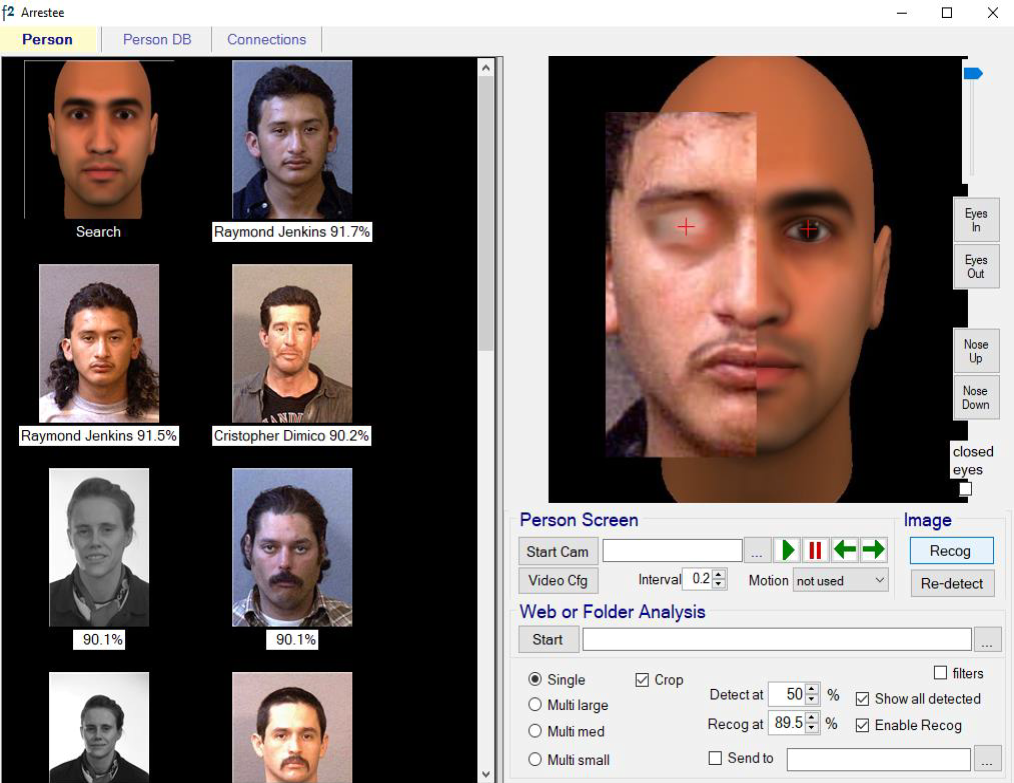
Partial face recognition is a module within the Face Forensics face recognition application. All the functionality of full face recognition is available to recognize and match the partial face. Selecting “Partial face” on a pull-down on the Face Screen displays a facial template.
A frontal shot is taken of the facial part. This image is either pasted or drag-and-dropped onto the facial template. The template itself is a computer-generated generic face.
Once the image is placed over the relevant area of the template it will have to be resized to match the size of the template. The template itself can then be adjusted to change the distance between the eyes, and the position of the nose. Once the partial face is deemed to be in the most realistic position the eye centres are manually selected and a search is initiated.
For more information CLICK on the button below to download the Partial Face Product Sheet.
 CLICK on the button below to download the Corpse ID Product Information Sheet.
CLICK on the button below to download the Corpse ID Product Information Sheet.
The f2 Tattoo Recognition Module is designed to match an unknown tattoo against a database of tattoos in order to identify its owner. It will also match a partial shot of a tattoo, e.g. where it’s partially concealed by clothing, against the full tattoos in the database. Results are displayed as thumbnails of potentially matching tattoos, in descending order of Match%. Any of these can be selected to display the face and name of the owner. Tattoo recognition is similar to biometrics like fingerprints, face, and iris recognition in the way the image is encoded and then matched.
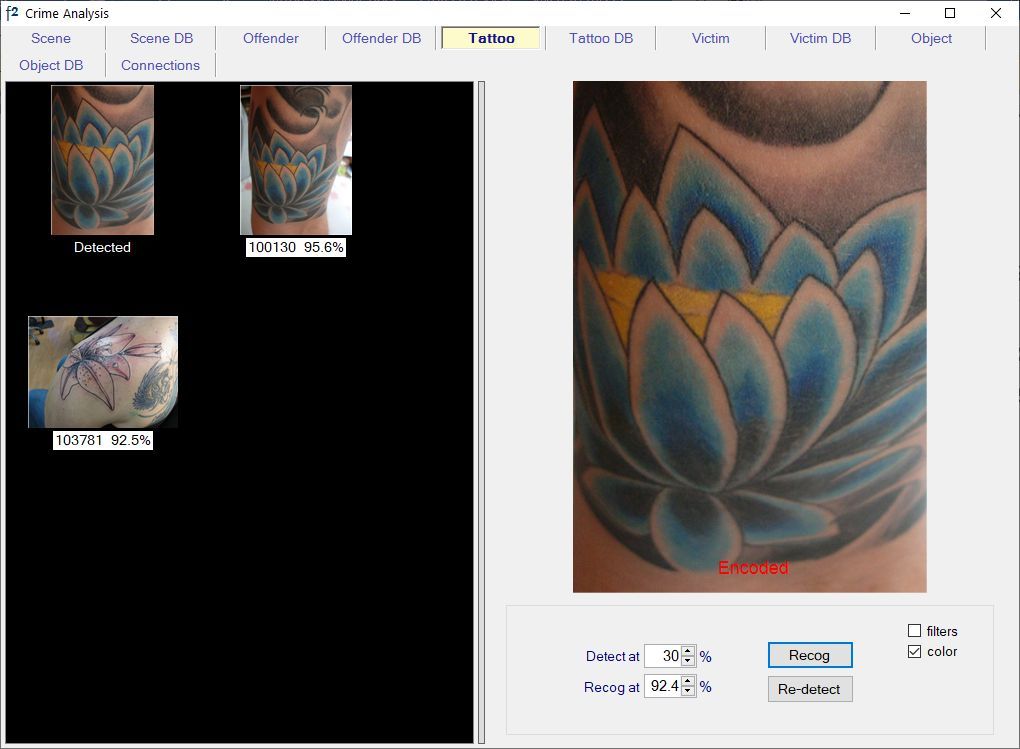
In the example above, the partial probe image is on the right and top matches are displayed on the left. f2 finds the single correct match in the 5700-tattoo database. The non-match below it is visually different to the probe but rates highly because it includes leaves of similar shape.
However it differs in that a tattoo can be of anything, and be of any shape and size in the image. f2 determines the unique characteristics of each, e.g. lines, curves, colors, etc, and their relative positioning. This means that the matchlist can contain tattoos which appear totally different to the probe image. This happens because the characteristics being searched for by f2 will often be present in other images that visually look quite different to the probe. However the correct match (assuming it’s in the database) should almost always be at or near the top of the list. f2 Tattoo is designed to work with images captured under controlled conditions and that meet NIST Tattoo Capture Guidelines. It is the perfect supplement to facial recognition.
Features:
- Matches complete tattoos and also those partially obscured
- Can also match scars and marks subject to sufficient detail
- Accesses images in existing external databases in read-only mode. (User can opt to store images.)
- Links a matched image back to its associated face and details in the original database
- Text (if included in the original record) can be used to help filter out non-relevant matches
- Automatic enrollment of all images in a database. No limit to database size
- Import and automatic enrollment of images in a folder
- Automatic detection and enrollment of new images added to an external database
- Probe and database images can match at up to 45° rotational difference
- Searches any database of enrolled tattoos on a VPN under appropriate controls
- Side-by-side comparison of “probe” image and potential match for visual inspection, including magnification
- Easy to install/use f2 Tattoo is an independent but fully integrated module within the f2 Suite.
CLICK on the button below to download the Tattoo Recognition Product Sheet.
Scene/Object Recognition (SOR) is a module within f2’s Image Recognition Suite. It’s designed to match virtually any solid object with distinguishing features against a database containing such objects and return the closest matches. It works similar to f2’s face and tattoo matching, i.e. a probe image is copied in and encoded using f2’s algorithms to produce a unique digital array which is then compared with all available images in the database. A key feature of SOR is its ability to identify objects which are a part of a larger object, often due to something else in front of it partly concealing it.
f2 has included a scene recognition module for some time now. However this was designed to match relatively large images, for example – rooms. Yet, there remained a clear need for object matching and a prototype module was developed for this. The experience gained emphasized that with minor modifications, such as image enhancement, the two modules could be combined into one.
SOR can process images from any source, including photos stored on PCs, and in the Cloud. It can process very large volumes of images even if they’re significantly obscured).
There’s no practical limit to the size of database that SOR can work with, subject to an appropriate hardware configuration.
- Ability to match objects in static images, video files, Cloud, and website images
- Ability to identify partially concealed objects
- Being able to link scenes with the same object in them
- Being able to optionally filter searches by dominant color, and text description if present
SOR does not actually match an image against other images; it matches a numeric string called an encode array describing the characteristics of an image against a database of encode arrays describing images. This increases speed, accuracy and minimizes the space required.
Within SOR the primary entity is the crime scene, i.e. a still shot or video frame. SOR analyzes the image to find multiple areas with strong contrasting features and transforms the characteristics of these mathematically into an encode array that uniquely identifies the image. The encode arrays for all the images in the database are in a master database in server memory.
(SOR comes with small sample databases of images to match against, so it can be tested immediately after installation).
f2 is a highly-advanced face detection and recognition system – the result of many years experience in the forefront of face recognition development. It will:
- Search a database to identify an unknown face
- Verify that an individual is who they claim to be
- Detect and recognize faces in a video stream
- Identify part of a face in a forensics or investigations environment
- Check an entire database, or multiple databases, for multiple records of the same person using different names, i.e. N:N matching
A major problem with almost any database containing records of people is that the same individual can have made multiple applications (e.g. for driver’s licenses, entitlement cards, etc), or have been arrested for a number of different crimes, using a different name each time. Face Forensics is specifically designed to enable instances of this to be easily identified. This applies to multiple records in the same database, and across different databases. The process involves first automatically encoding all the facial images in one of the databases. Then each image in the other database is encoded and matched against each in the first. While this can take some time (depending upon the size of the databases) the process is fully automatic and can be left to run until the task is complete. All possible matches, i.e. above a user-defined threshold, are sent to a separate folder for subsequent review.
Face Forensics is available as an application or .NET SDK. It runs under 64-bit Windows 10. It will access SQL Server databases. An evaluation version is available.
For more information contact: Contact@SketchCop.com
CLICK on the button below to download the Multiple Person Search Product Sheet.
